Authentication with OpenID
- name:
- OpenID Authentication
- description:
- SSO User authentication and User provisioning using oAuth or OpenID
- version:
- 1.2.4
- release:
- 2025-01-23
- itop-version-min:
- 3.2.1
- code:
- combodo-hybridauth
- state:
- stable
- php-version-max:
- PHP 8.2 since version 1.2.1. PHP 8.0 otherwise
With this extension, users can connect to iTop using OpenID providers (Facebook, Google, Twitter, LinkedIn, MicrosoftGraph …)
Features
Add capability to configure SSO authentication with most common OpenID Identity providers (Facebook, Google, Twitter, LinkedIn, MicrosoftGraph …)
-
It offers new authentication modes based on oAuth and OpenID Single Sign On (SSO) for the following OpenID providers:
-
Those modes can be mixed with other modes (internal, SAML …)
-
It is possible to configure several Identity providers if you want to allow access for instance to both Google and MicrosoftGraph
-
It relies on HybridAuth library library, which provides a unified interface to identify a user and retrieve contact information.
-
Some of those Identity providers are able to provide user information to allow automatic User and Person provisioning in iTop.
Check the third column of the Providers table, it is required for automatic User/Person provisioning on User first connection.
Revision History
| Version | Release Date | Comments |
|---|---|---|
| 2025-01-23 | 1.2.4 | * N°7807 - Add support for organization selection
during autoprovisioning * N°7673 - Oauth2 for webhook * N°6088 - New attribute AttributeEncryptedPassword * N°7932 - Add english (GB) translation to iTop * Add EN GB dict file (#5) |
| 2024-09-03 | 1.2.3 | * N°7780 - 'allowed_login_types' order doesn't work for authentification with OpenID |
| 2024-08-02 | 1.2.2 | * N°7582 - Be able to tune debug configuration from UI |
| Not published | 1.2.1 | * N°7088 - Authentification OAUth2 with
Keycloack * N°6346 - combodo-hybridauth : update library for php 8.0 compatibility * N°4473 - Add delegated authentication (OpenID) configuration GUI |
| 2023-11-28 | 1.2.0 | * N°6556 - Add possibility to customize display of login buttons |
| 2023-07-13 | 1.1.2 | * N°6509 - Remove tests folder from builds |
| 2023-07-05 | 1.1.1 | * N°6369 Fixing warnings when configuration is
missing * Updated german translations by Lars Kaltefleiter |
| 2022-12-02 | 1.1.0 | * Compatibility with iTop 3.0 |
| 2019-08-27 | 1.0.0 | * First version |
Limitations
There is no mapping capability for contact provisioning.
This capability may not work if you have changed the default datamodel
Requirements
You have to configure the iTop application on your Identity provider to allow communication between iTop and this one. Look at your Identity provider documentation for more details.
Installation
Use the Standard installation process for this extension.
Configuration
First, you have to configure the iTop provider on your identity provider (Google, Facebook …)
-
The iTop landing page to provide to your Identity provider is:
<itop url>/env-production/combodo-hybridauth/landing.php
Once iTop is configured,
-
open the file 'config-itop.php'
-
add to the
allowed_login_typesparameter, the corresponding provider in the form of hybridauth-<provider name>
- config-itop.php
-
allowed_login_types => 'form|hybridauth-Facebook|hybridauth-Google|hybridauth-MicrosoftGraph|basic|external',
-
formmust remain the first, for all the others to be proposed to the user. -
If an hybridauth option is entered first, then the login page directly jump to the remote provider login page.
basicmust be left in the list for REST to still work.
The configuration is located in the section
combodo-hybridauth.
In the providers section you can configure several providers. The
“enabled” flag allows to activate the each authentication provider
or not
| parameters | description | values |
| debug | active the logging mode. All logs are written in the file log/hybridauth.log under iTop directory | true or false |
| synchronize_user | define if user provisioning is active | true or false |
| synchronize_contact | define if contact provisioning is active, recommended if you have configured user provisioning | true or false |
| default_organization | default organization used to create a contact | an iTop existing organization name |
| default_profile | profile name given automatically at user creation | an iTop profile |
For each provider, you have to specify the application id configure on the provider side, and the secret for authentication
It should look as shown below:
Example of a configuration in which Google is configured but deactivated and MicrosoftGraph is activated:
- config-itop.php
-
'combodo-hybridauth' => array ( 'debug' => true, 'synchronize_user' => true, 'synchronize_contact' => true, 'default_organization' => 'demo', 'default_profile' => 'Portal User', 'providers' => array ( 'Google' => array ( 'enabled' => false, 'debug' => true, 'keys' => array ( 'id' => 'your-google-client-id', 'secret' => 'your-google-client-secret', ), ), 'MicrosoftGraph' => array ( 'enabled' => true, 'debug' => false, 'keys' => array ( 'id' => 'xxxx-xxxxx-xxxxx-xxxxx', 'secret' => 'xxxxxx', ), ), ), ),
Specific settings by provider (since version 1.2.1 N°4473)
Options set globally in the module section, can be override for a specific provider:
-
default_organization,
-
default_profile,
-
synchronize_user,
-
synchronize_contact
| parameters | description | values |
| synchronize_user | define if user provisioning is active | true or false |
| synchronize_contact | define if contact provisioning is active, recommended if you have configured user provisioning | true or false |
| default_organization | default organization used to create a contact | an iTop existing organization name |
| default_profile | profile name given automatically at user creation | an iTop profile |
| enabled | define wether the provider is enable or not. Caution you also have to remove the configuration from allowed_login_type, else the button remain on the authentication form | true or false |
| label | label used on the authentication button for the corresponding provider. Use the default one if not set | |
| tooltip | tooltip displayed when the use move over the button for the corresponding provider | |
| icon_url | a url, a path to the icon in iTop or a fontawesome | exemples https://itop url/images/icon.png or images/icon.png or fas fa-key |
Example with Google here, that describes how to use different profile and organization for a given provider:
'combodo-hybridauth' => array (
'debug' => false,
'synchronize_user' => false,
'synchronize_contact' => false,
'default_organization' => 'GlobalOrg',
'default_profile' => 'Configuration Manager',
'providers' => array (
'Google' =>
array (
'keys' =>
array (
'id' => 'id',
'secret' => 'secret',
),
'enabled' => true,
'synchronize_user' => true,
'synchronize_contact' => true,
'default_profile' => 'PortalUser',
'default_organization' => 'IT Department',
),
),
),Issue with consent form always displayed with Google/MSGraph (regression N°8235 in version 1.2.4 only)
Even when remaining connected on Identity provider (Google/MSGraph only), consent form is proposed each time you click on login button. in versions < 1.2.4, the form was not displayed and user was immediately logged in.
Workaround (Google/MSGraph only): add authorize_url_parameters section as proposed in below example
'combodo-hybridauth' => array (
...
'providers' => array (
'Google' =>
array (
'enabled' => true,
'authorize_url_parameters' =>
array (
'prompt' => '',
),
...Usage
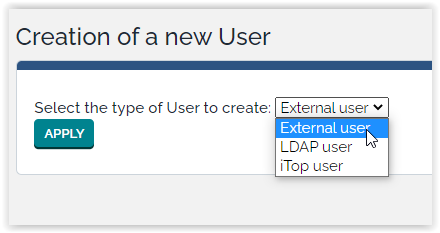
If you don't use the automatic provisionning, you have to create in iTop SSO users using the type External user when prompted for a “New user Account”:
Once configured, the Login form will look like
Provisionning
If you activate the User/Person provisioning, here is what will be filled automatically with what the hybridauth provider returns (Not all data are provided by each provider)
-
Person fields provisioned regardless of the Provider:
first_name,name,email,phone,org_idwith the fixed value from the Configuration File -
User field provisioned:
login,person_id
The rest of the fields got their default value.
If the iTop standard datamodel was changed by adding mandatory field without default value on User and/or Person, this can break the provisioning
Questions & Answers
Q: Can I mix OpenID Connect and a captcha?
A: Yes this is possible using the Combodo's customer extension
Brute Force Protection.
Q: What is Hybridauth, OpenID Connect and
OAuth2?
A:
-
Hybridauth is the PHP library used by iTop to run the OpenID Connect protocol
-
OpenID Connect is the 3rd version of the OpenID protocol, it uses OAuth2, it's a protocol used exclusively for Authentication and user provisionning
Q: Can we change the layout of the login page (name,
button,…)?
A: Since version 1.2.0 (inclued in iTop pro 3.1.1) this is possible
to customize the label, tooltip and icon on the buttons.
For example, if you would like to change the label and the icon to
connect to google provider you can replace de default button by the
one below

Define in module section theirs settings:
- config-itop.php
-
'combodo-hybridauth' => array ( 'debug' => false, 'synchronize_user' => false, 'synchronize_contact' => false, 'default_organization' => '', 'default_profile' => 'Portal User', 'providers' => array ( 'Google' => array ( 'enabled' => true, 'label' => 'Login like a bear', 'tooltip' => 'Login with your paw', 'icon_url' => 'fas fa-paw', 'keys' => array ( 'id' => 'your-google-client-id', 'secret' => 'your-google-client-secret', ), ), ), ),
In this case, you will see on the button the label you set +
provider name (automatically added after your label).
If you want to hide provider used to connect, you will need to use
dictionary entry in your configuration file and set values in all
languages you used to this dictionary entry.

- config-itop.php
-
'combodo-hybridauth' => array ( 'debug' => false, 'synchronize_user' => false, 'synchronize_contact' => false, 'default_organization' => '', 'default_profile' => 'Portal User', 'providers' => array ( 'Google' => array ( 'enabled' => true, 'label' => 'Google:HybridAuth:Login:SignIn', 'tooltip' => 'Login with your paw', 'icon_url' => 'fas fa-paw', 'keys' => array ( 'id' => 'your-google-client-id', 'secret' => 'your-google-client-secret', ), ), ), ),
Q: Can we implement several connexion for a given
provider to implement several tenant?
A: Since version 1.2.0 (inclued in iTop pro 3.1.1) this is possible
to configure several connexion to different tenant using the same
provider.
In the example below we configure connexion with
MicrosoftGraph to TENANT1 and
TENANT2
You have to configure the module combodo-hybridauth to define 2 providers using the same adpater (method to access the provide). It is MicrosoftGraph in our example.
The code TENANT1 and TENANT2 are the idenfier that will be used in the variable allowed_login_type to allow those connexions
You can specify application id and secret corresponding to your tenant and define label, tooltip and icon specific to help the user to chose the good connexion method.
- config-itop.php
-
'combodo-hybridauth' => array ( 'debug' => true, 'synchronize_user' => false, 'synchronize_contact' => false, 'default_organization' => '', 'default_profile' => 'Portal User', 'providers' => array ( 'TENANT1' => array ( 'adapter' => 'Hybridauth\\Provider\\MicrosoftGraph', 'label' => 'Authentification On Tenant 1', 'tooltip' => 'Connexion from O365 - Tenant 1', 'enabled' => true, 'keys' => array ( 'id' => 'MyApplicationIdOnTOnMyTenant-1.fr', 'secret' => 'MySecretOnMyTenant-1', ), 'synchronize_user' => true, 'synchronize_contact' => true, 'tenant' => 'MyTenant-1.fr', 'default_organization' => 'MyCompagny', ), 'TENANT2' => array ( 'adapter' => 'Hybridauth\\Provider\\MicrosoftGraph', 'label' => 'Authentification On Tenant 2', 'tooltip' => 'Connexion from O365 - Tenant 2', 'enabled' => true, 'keys' => array ( 'id' => 'MyApplicationIdOnTOnMyTenant-2.fr', 'secret' => 'MySecretOnMyTenant-2', ), 'synchronize_user' => true, 'synchronize_contact' => true, 'tenant' => 'MyTenant-2.fr', 'default_organization' => 'Demo', ), ), ),
In this case, the provider 'TENANT1' gives access to iTop with a MicrosoftGraph connexion to MyTenant-1.fr, and the provider 'TENANT2' to MyTenant-2.fr
in your configuration file, you have to add values hybridauth-TENANT1 and hybridauth-TENANT2 in field allowed_login_types:
- config-itop.php
-
'allowed_login_types' => 'url|form|hybridauth-TENANT1|hybridauth-TENANT2|external|basic',
https:<itop server>/pages/UI.php?login_mode=hybridauth-TENANT1 if you have a large number of tenant, for instance one by customer, you can use this syntaxe in an html page where you display the url for each tenant in order to route the user to the good one </note>